Things I Learned About Domains from My Interview with Tomasso and Alessandro, the Wines.xyz Father-Son Duo
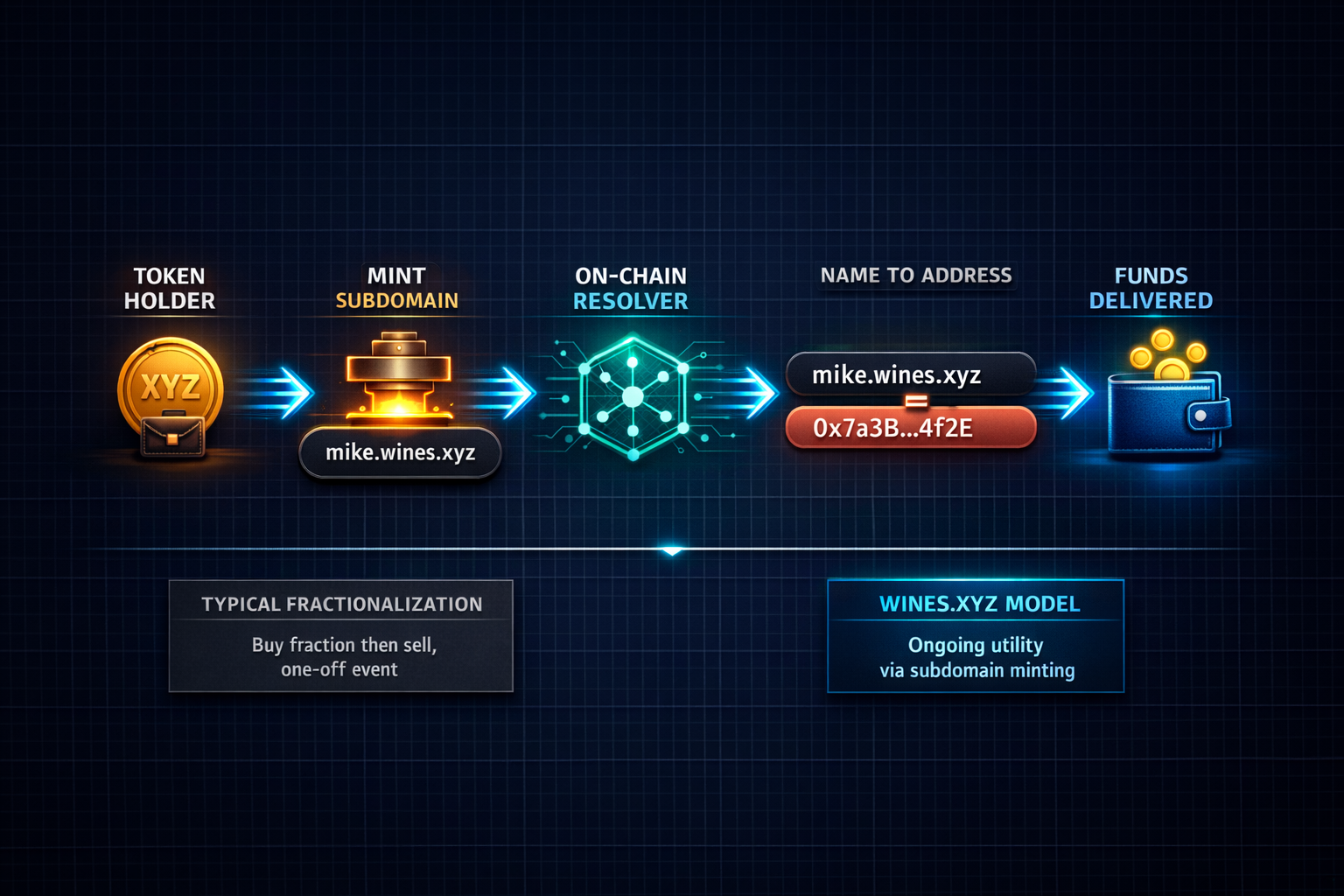
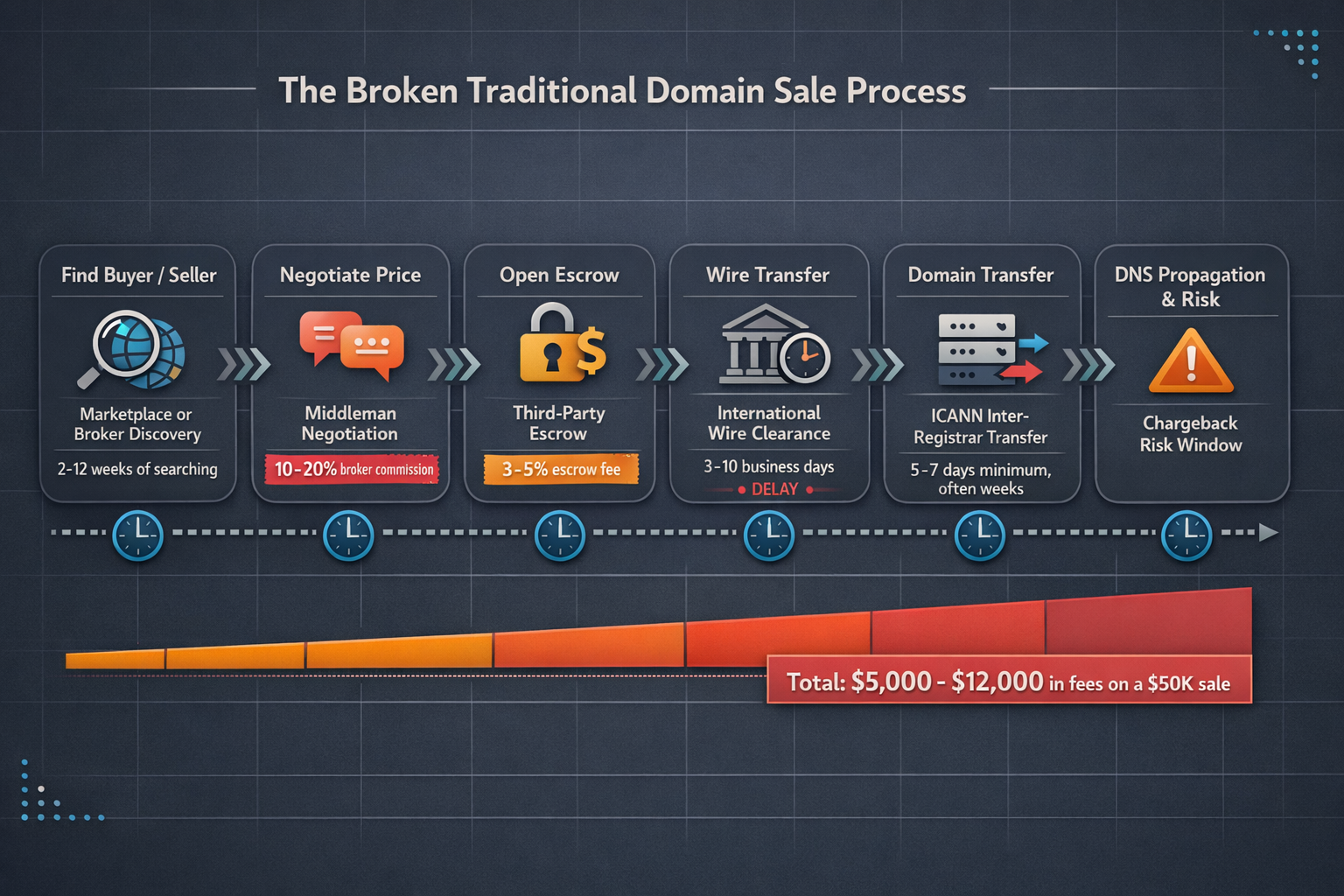
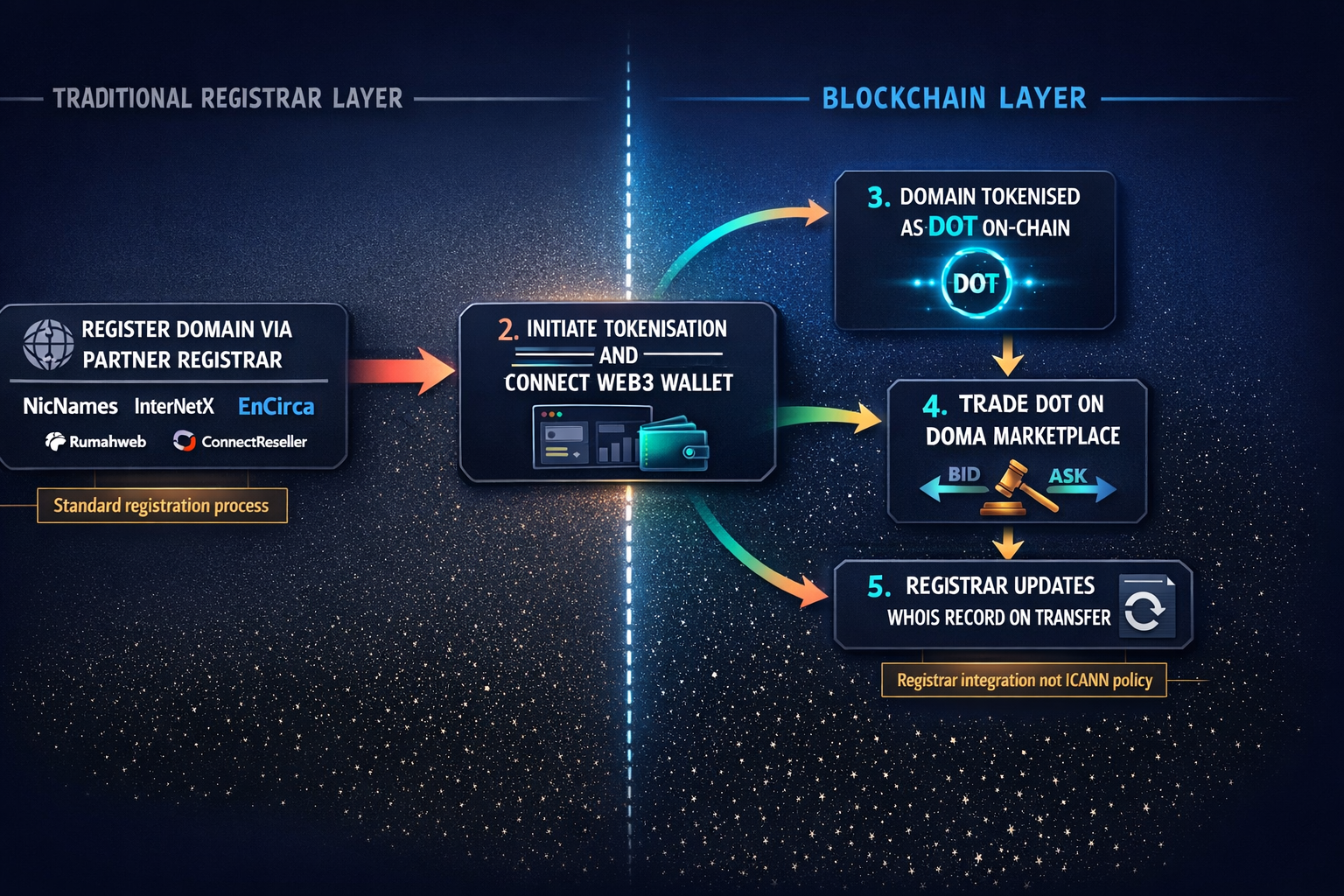
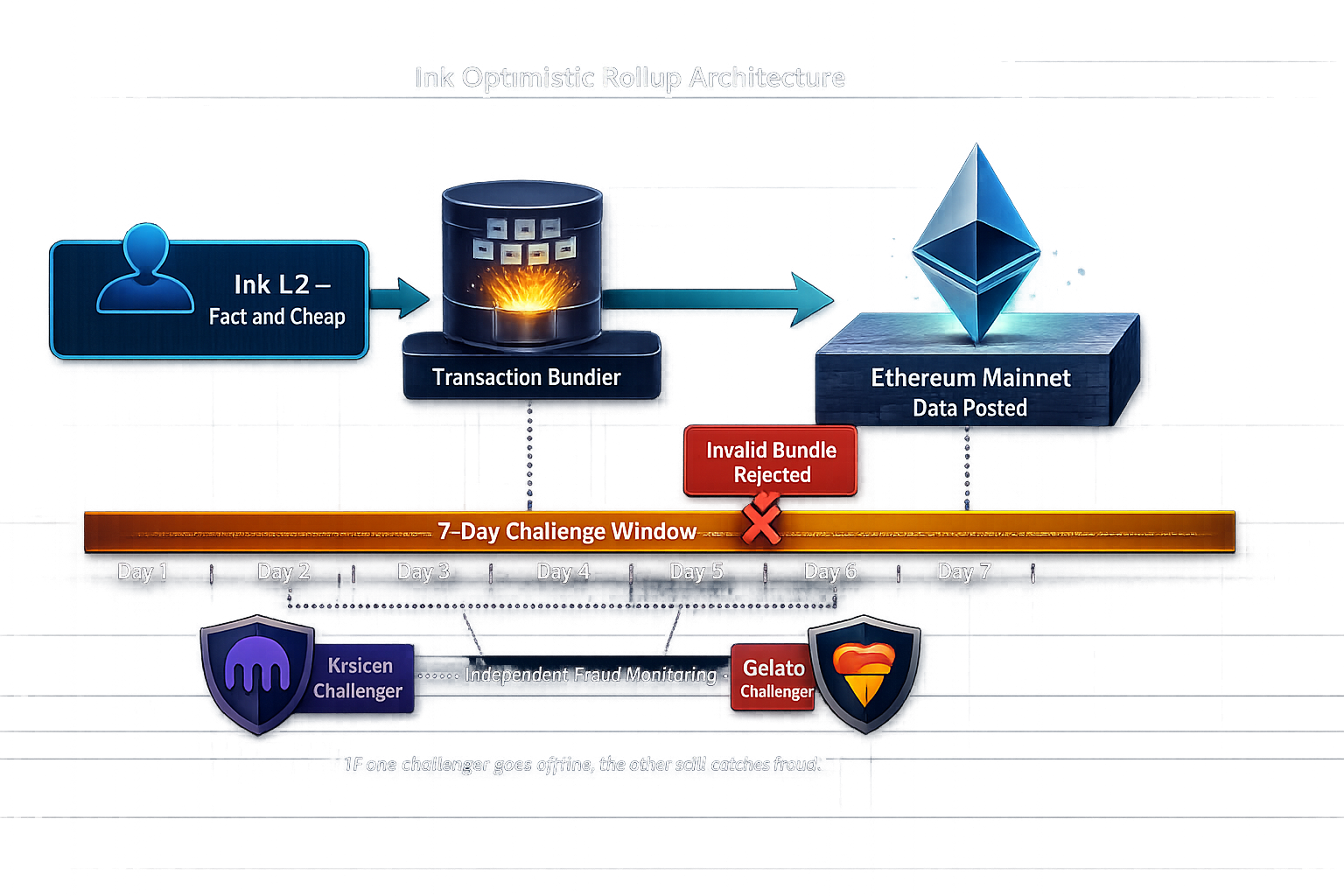
Covers domain tokenization via Doma Protocol through the Wines.xyz case study, including investment filters, subdomain utility, and onboarding realiti…